Blog
Who is in your hospital right now? Where are they going, and why?
by Paul Kazlauskas
3 new eVisitor software security features help manage your visitor capacity.
Your hospital’s visitors, vendors, and contractors come and go. If you don’t know who they are, where they’re going, and why, you’re exposing your people and property to considerable harm.
eVisitor is a robust, yet simple visitor management software system that is easy to use. The software solution is reasonably priced and has flexible options, so you buy only what you will use. It has reliable, cloud-based data access for easy implementation on current Windows-based computers.
We are excited to announce 3 new software features that will help users manage their visitor capacity even better than before!

(1) Room-Track™ alerts you to how many visitors are in a room and who they are. As soon as you enter a room number, the red text appears as shown (if there are visitors already signed in to that room).
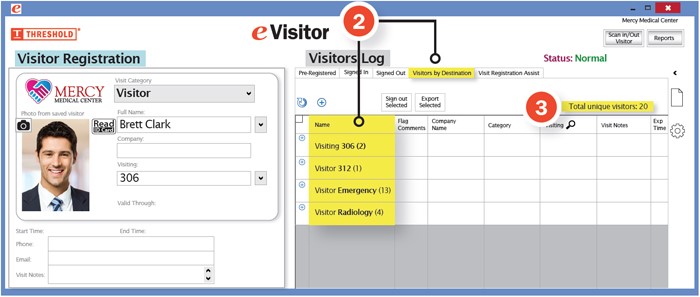
(2) The Visitors By Destination tab shows a list of all destinations that have visitors and the number of visitors in each. When you click on one of the rooms, you see who is visiting.
(3) Total Unique Visitors (also above) shows you at a glance how many visitors are in your entire facility.
Request a free demo of eVisitor Software
We will contact you to schedule an online appointment. If you have any questions, please call 800-243-1969. Thank you for your interest!
Want the latest, best security practices delivered straight to your inbox? Click the "Subscribe to the Blog" button (on the left side navigation).
Posted on 9/3/2020



 Paul Kazlauskas
Paul Kazlauskas
 Andrew Jones
Andrew Jones