Visitors to an office building come in many different forms. A few different types include business guests, potential new hires, delivery personnel, and employee family members. Some visitors are regulars, while others visit just once and are never seen again in the facility. Regardless of what business you’re in, there are certain security issues you need to address with regards to visitors. Here 9 tips and procedures for keeping your facility secure:
1. Decide on an authorization protocol.
Who has the authority to approve visitors to the office? It depends on the type and size of the organization. Many times, any employee who will be meeting with a visitor has the authority to admit that visitor. Other times, the responsibility may fall to the security department or a receptionist. Occasionally, a manager may need to actually authorize a visitor for their employee, depending on the type of facility and what kind of work is done there.
2. Determine which areas of the building are open to visitors.
A comprehensive visitor policy should take into account which areas of the facility are open to visitors and which are not. This can vary by the type of guest. For example, an HVAC repairperson would have access to different parts of the building than a sales rep coming to try to sell a new server to the I.T. department. Conference rooms may be open to all types of visitors, but the manufacturing floor may be off-limits to all but a select few because of competitive secrets. The lobby should be open to all visitors, but it is common to have some type of restriction beyond that area, depending on the type of visitor.
3. Document visitor traffic using visitor management software.
Visitor management software is an electronic version of the visitor sign-in sheet (or visitor log book) that has been used in buildings for years and is being implemented more frequently in the business world. While more expensive than a traditional log book, a VMS offers a more efficient and full-proof sign-in process. It is the most secure way to sign in visitors that come to your office and a very affordable way to improve the visitor management and security of your company. Visitor management software allows you to:
- Know who is in the building at any day/time
- Provide a standard way to register visitors
- Print professional-looking visitor badges that include critical information
- Improve your company’s bottom line
4. Add a Visitor Agreement/Limited Liability Statement on the visitor badge.
This security practice allows the organization to clearly state what is expected of the visitor while on it’s property. This statement could include everything from protecting trade secrets within the facility to declaring to what extent the organization is liable for any injury that may occur. The organization has its bases covered if it requires visitors to agree to this statement as they sign in while entering the facility.
5. Choose how to identify visitors.
The electronic visitor management system mentioned above will provide your guest with a visitor badge to clearly identify them as such. Some visitor badges change color overnight to prevent reuse. These special visitor passes provide a visual alert to the security staff or employees that a person’s presence should be questioned. If your visitor doesn’t want to use the adhesive badge directly on their clothing, badge tags can be utilized in conjunction with a badge clip. Badge tags are laminated holders for the adhesive badge (some are even reusable).
6. Identify various kinds of visitors in a specific way.
As mentioned earlier in this post, different kinds of visitors have different access to certain areas of the building and therefore may require different treatment and identification. Clearly identifying the type of visitor will allow anyone encountering that person to know if they are allowed to be in the area. Vendors, contractors, temporary workers, interns, interviewees, and family of employees are all categories to consider. You should have a badge template for any type of group coming to your building.

7. Guarantee visitors are escorted while in the office.
Office guests should be welcomed as long as their reason for being there is legitimate and they are authorized by the appropriate person. However, upon entering the facility, the visitor should be escorted to the area/people that they are there to see.
8. Train your staff about the office visitor policy/procedure.
Once you’ve created a company-wide visitor policy, it is imperative to train your staff. Training and periodic test drills will ensure your employees are familiar with and confident in the security policies in place. This training includes a clear set of guidelines that covers how employees are supposed to act. Topics include everything from what to do if they see an undocumented visitor to what to do if they see a fellow employee violating the procedure.
9. Make visitors feel welcomed.
A lot of effort and planning goes into a security plan for what to do with individuals when they arrive on-site, but what about from the visitor’s point of view? Are visitor’s needs being addressed? Here are some ways to improve the experience of visitors when they come to your facility and to answer their questions about what to do once they arrive:
- Communicate with visitors, before their planned visit, directions for getting to the facility, where to park, and what entrance to use.
- Once at the facility, provide signage explaining where to go.
- Create an inviting lobby with comfortable chairs, refreshments, and up-to-date reading materials while they wait.
- Follow up after your visit to see if there are any areas of improvement for their visitor experience.
https://rcphotostock.com – © rcphotostock (10399)
A great tool for improving facility security is a visitor management system. eVisitor Software is a stand-along visitor management systems that can affordably increase your facility security and help you always know who is in your building. eVisitor makes it easy for facilities to log, identify, track, and run reports on visitors. Watch this video to learn more, then request a free demo today!







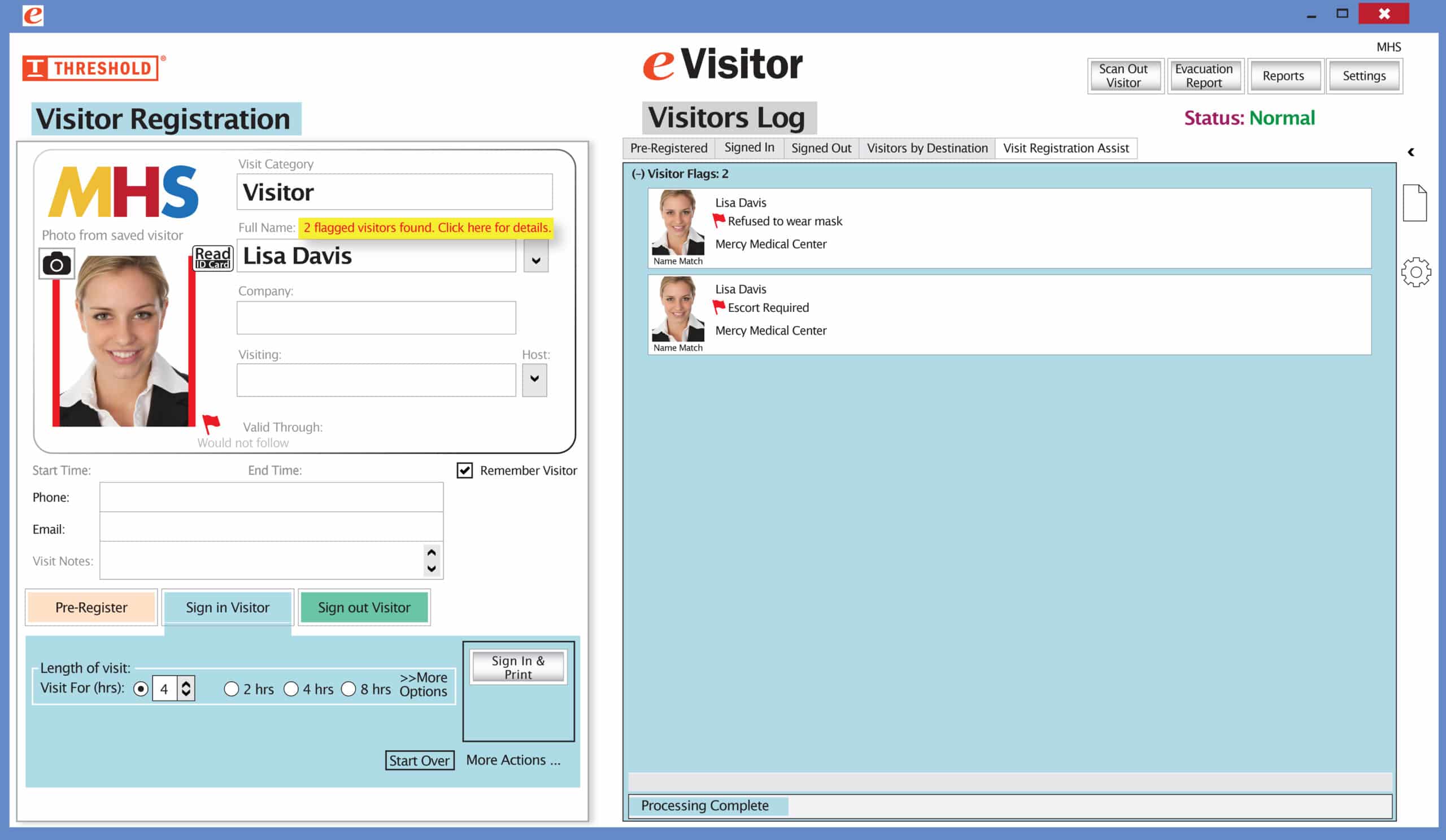 It’s easy and free to activate this feature. Simply call us and ask for “Red Flag, No Badge” to be turned on. Once it’s on, the above pop-up will come up when a red flagged visitor comes back. No badge will print and the attendant will need to follow the facility’s policy for handling red flagged visitors.
It’s easy and free to activate this feature. Simply call us and ask for “Red Flag, No Badge” to be turned on. Once it’s on, the above pop-up will come up when a red flagged visitor comes back. No badge will print and the attendant will need to follow the facility’s policy for handling red flagged visitors.